Directory Access Changes allows your servers to record (when possible) both the old and the new values of an object after a change. This means that if a value was incorrectly changed, the old value may be record in your audit log. To configure this, you would have to log into each server and type:
Auditpol /set /subcategory:”Directory Service Changes” /Success:Enable
For one or two servers, this is OK. For hundreds, this is a problem. You can utilize Group Policy to configure this on each of your servers/clients.
Either create a new GPO, or use an existing one that is scoped to your requirements.
Expand Computer Configuration \ Policies \ Windows Settings \ Advanced Audit Policy Configuration \ Audit Policies \ DS Access
Double click Audit Directory Service Changes.
Check Configure the following audit events.
Check Success and/or Failure
Click OK.
Once this policy is applied and your clients/servers refresh their Group Policies, you can test this GPO.
On a client/server that had this policy applied, click Start. Type cmd and press Enter.
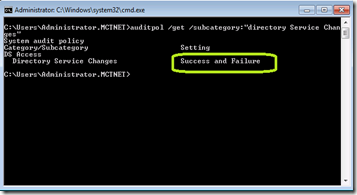
Type auditpol /get /subcategory:”Directory Service Changes” and press Enter.
You should see the configuration that you set.

Comments